7.1 Networks
|
Previous
Chapter 6: Social implications of hardware
|
Next
Chapter 8: Social implications of computer networks
|
 CHAPTER OVERVIEW
CHAPTER OVERVIEW
| Unit 7.1 | Networks |
| Unit 7.2 | Intranet vs internet |
| Unit 7.3 | Basic network security |
| Unit 7.4 | Internet services |
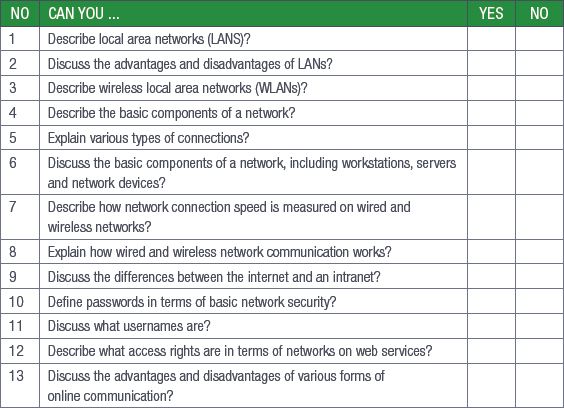
 By the end of this chapter, you will be able to:
By the end of this chapter, you will be able to:
- Describe local area networks (LANs)
- Discuss the advantages and disadvantages of LANs
- Describe wireless local area networks (WLANs)
- Describe the basic components of a network
- Explain various types of connections
- Discuss the basic components of a network, including workstations, servers and network devices
- Describe how network connection speed is measured on wired and wireless networks
- Explain how wired and wireless network communication works
- Discuss the differences between the internet and an intranet
- Define passwords in terms of basic network security
- Discuss what usernames are
- Describe what access rights are in terms of networks on web services
- Discuss the advantages and disadvantages of various forms of online communication

Something to know
In 1973, the Defence Advanced Research Projects Agency (DARPA) in the United States began researching the techniques and technologies needed to develop communication protocols that would allow computers in the same network to communicate with each other across multiple linked networks. This was called the “Internetting” project and it resulted in what we know as the internet today. This was also the first functioning example of LANs communicating with each other. Before this, computers could only communicate with each other if they were connected in the same network.
INTRODUCTION
In Grade 10, you learned about home area networks (HANs) and personal area networks (PANs). HANs are very small networks that usually cover a single home. PANs, on the other hand, are much smaller and are usually designed to serve a single user.
In this section, you will learn about local area networks and wide area networks and how they are generally used.

NETWORKS AND INTERNET TECHNOLOGIES
What is the difference between the internet, a network, and an intranet?

UNIT
7.1 Networks
In this unit, you will be focusing on:
- LANs and WLANs
- Basic network components
- Network software
- Network connections
- Network communication
TYPES OF NETWORKS
LOCAL AREA NETWORKS
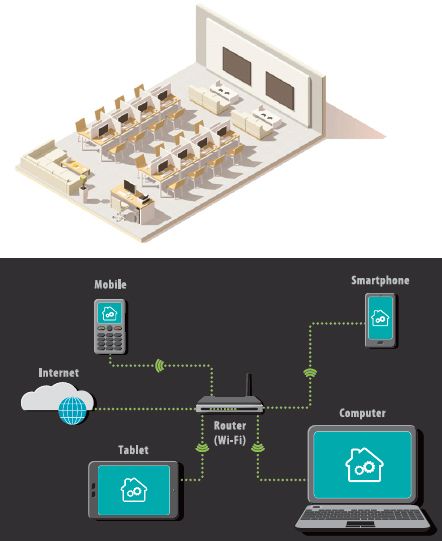
A local area network (LAN) is a small network of computers covering a small area, such as an office building or school. A wireless local area network (WLAN) is the same as a LAN but it has the ability to connect wireless devices such as smartphones, laptops and tablets to the LAN.
LANs may serve only one or two users (for example in a home) or they can serve hundreds of users (in an office building or on a school campus). No matter how many users LANs serve, they are all designed to share resources such as internet connections, printers or server connections. Most LANs use either wireless or wired connections or a combination of the two to connect devices. For example, desktop computers and laptops can be connected to the network with cables while the printer and mobile devices are connected using wireless connections.
LANs have several advantages and disadvantages.
Some of the advantages of LAN are:
- Software (and licenses), files and hardware can be shared easily with the devices connected to the network.
- Files and other data can be shared faster if they remain on the network and do not need to be uploaded to the internet or emailed.
- Networks can be centrally controlled, making it easier to make changes, monitor users, update software, troubleshoot hardware and software issues and maintain resources.
Some of the disadvantages of LAN are:
- The initial setup costs for creating a network can be high, especially in a school or office environment, as you need to make sure that you have enough resources for the number of computers.
- There is a risk of privacy and data violations. Network administrators may have access to all the files created by each user.
- If a network is not secured properly, one infected computer can infect the entire network.
WIRELESS LAN (WLAN)
A wireless LAN (WLAN) is a wireless computer network that links two or more devices using wireless communication to form a local area network (LAN) within a limited area such as a home, school, computer laboratory, campus, office building etc. This gives users the ability to move around within the area and yet still be connected to the network. A WLAN allows users to move around the coverage area, often a home or small office, while maintaining a network connection.
BASIC COMPONENTS OF A NETWORK
A network consists of the following basic components:
- Workstation and servers
- NIC
- Network devices
- Communication media
- Network software
WORKSTATIONS, CLIENTS AND SERVERS
Workstations and servers are usually part of a network. Workstations are the computers connected to the network. They are used by people to carry out tasks, for example the accountant who creates spreadsheets or the designer who designs websites.
Workstations will have input and output devices because they are designed to be used by humans. Some workstations, such as those designed to run computer-aided design (CAD) applications, will be more powerful than the computers you can buy to use at home.

Servers are designed to manage network resources and hardly ever carry out tasks beyond their server tasks (for example, you would not use a server to design an advertisement).
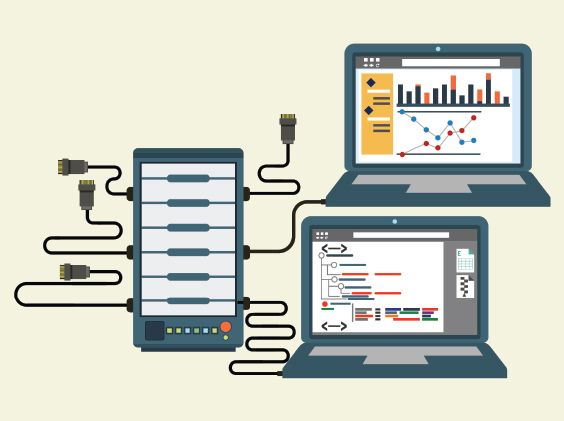
The main function of a server is to serve the information stored on it to other computers that are connected to it by a network. A server will usually have more RAM than a normal computer so that it can process data faster and it will use special operating systems, such as Linux and Windows Server, to carry out its tasks. Servers also usually have faster CPUs and larger hard drives, and they are often connected to UPSs.
Servers are usually only used for one type of task, for example:
- Email servers send and receive emails and store each user’s email information (their email address, username and password). Email servers can be local, such as those used by businesses, or global, such as Gmail. You interact with email servers through an email client, such as Microsoft Outlook or Gmail.
- Web servers are where the World Wide Web is. You will use a web browser, such as Google Chrome or Internet Explorer, to interact with a web server. Web servers deliver web pages to you when you request them, but they are also where you can upload data to cloud storage systems or your own website.
- Database servers are usually local servers that cannot be accessed by users outside the network they are connected to. Users can access database servers using specialised software (such as Microsoft SQL) to interact with them.
- A file server is a computer responsible for the central storage and management of data files so that other computers on the same network can access the files.
Some networks have a dedicated server which serves workstation (called clients). This is known as a client-server network. Other networks have workstations (called nodes) which act as both server and client. This is known as a peer-to-peer network.
NETWORK INTERFACE CARDS
Network interface cards (NICs) are pieces of hardware that allow a computer to connect to a network. Most modern computers have this device integrated into their motherboards, but NICs can also be purchased separately.

Network interface cards are also called network interface controllers or network cards. An NIC connects using ethernet cables, while a wireless NIC (WNIC) uses an antenna to connect to a wireless network. Smartphones use WNICs to connect to data signals and Wi-Fi hotspots. Laptops and desktops can use both NICs and WNICs to connect to a network.

Something to know
Network cards that plug into a computer or laptop using a USB cable are not NICs. They are called network adapters.
CONNECTION DEVICES
For a network to function, it needs some of the following:
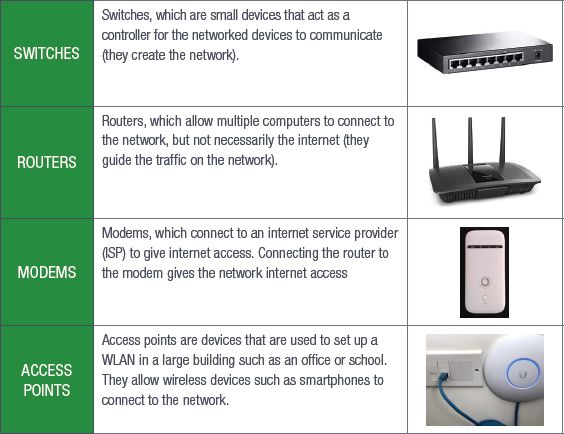
Most modern routers combine the modem and the switches. A modem is a communication device. Modems are hardware devices that connect a computer or router to a broadband internet network. They work by converting the digital data sent by the computer into the analogue signal used by telephone lines. Modems are classified by how much data they can send (in bits per second) and how they connect.
Early modems used a dial-up connection to communicate but now they use digital connections (digital subscriber line, or DSL), fibre or wireless.
NETWORK SOFTWARE
Network software refers to a range of software aimed at the design, implementation and operation of computer networks. It exposes the inner workings of the network to the network administrators, assisting them in managing and monitoring the network. It also allows multiple devices such as desktops, laptops, tablets, mobile phones and other systems to connect to each other as well as to other networks.
It is important that you understand the difference between network software and software applications. Network software is mostly used by network administrators, while software applications allow users who are working within a network to do their work.
If your network has a server, that server will need a server operating system. You can choose between different types of server operating systems to suit your needs. Device management software will allow you to manage all the devices connected to a network.
The functions of network software can be summarised as follows.
- Its main function is to set up and install computer networks.
- It allows network administrators to add or remove users from a network.
- It helps administrators to protect the network from data breaches, unauthorised access and attacks on a network through the use of a security tool.
- It helps administrators to define locations of data storage and allows users to access that data.
COMMUNICATION MEDIA
Network connections can be wired or wireless. Wired network connections use ethernet cables to connect all the devices in a network, such as the computers, routers and switches. Ethernet cables are made up of several twisted pairs of wires inside a plastic casing and have a connector on either end called an RJ45 connector, which plugs into network ports on the various devices.


ETHERNET VS WI-FI
Wireless networks use radio signals to connect all the devices in a network (such as the computers, routers and printers). When you connect to a Wi-Fi hotspot in a restaurant or hotel, you are connecting to a wireless network.
HOW FAST IS MY NETWORK?
Wired and wireless networks can only transfer data as fast as their connections allow. The speed at which a network can transfer data is based on its components.
WIRED SPEEDS
For wired networks, the speed of the network is determined by the rated speed of the cables you use. The most common cable speed is 1 Gb (gigabit), these cables can transfer 1 000 Mb data per second.
WIRELESS SPEEDS
The speed of wireless networks depends on the standards they use. Wi-Fi standards are certified by the Institute of Electrical and Electronics Engineers (IEEE). The main IEEE standard for wireless networks is 802.11 and there are a number of specifications under this banner.
The 802.11 standards are different in terms of speed, transmission ranges and the frequency they use, but there are only a few of these standards that you will need to know. These standards make it easy for you to know what speeds you can expect from a given wireless access point (WAP).
LOOKING AT ADVERTISEMENTS FOR NETWORK DEVICES
Now that you have a better understanding of what a LAN is and how they are created, you will be able to take what you have learned and use it to interpret advertisements for network devices. There are several key pieces of information you will need to look out for when it comes to deciding which networking devices you want to buy.
Look at the rated speed for NICs and cables and match them to make sure that your data is transferred as quickly as possible. Make sure that WNICs are using the newest wireless standard (802.11ac).

On routers, check the number of ports, whether it is able to handle wireless connections, how many networks it can connect and whether or not it has a built-in modem.
Lastly, look at how well these devices meet your requirements and how suitable a connection type is to the space available (work out if a wired or wireless connection would be better).

Something to know
Remember: The frequency of the bandwidth determines how much data can be carried through a specific network at any given time. A one GHz connection is equal to a 1 000 MHz connection.
NETWORK COMMUNICATION
Now that you understand how networks are connected, you need to understand how the different components of a network communicate with each other. Wired and wireless networks use very different communication media to connect the various components.
WIRED COMMUNICATION
There are two types of cables that connect modern wired networks to each other, namely unshielded twisted pair (UTP) cables and fibre optic cables. UTP cables are commonly used to connect LANs and telephone networks as they are easy to make and set up and are relatively cost-effective.
They are made up of two cables that are twisted together (the twisted pair) to cancel out electromagnetic interference from outside sources. They are called unshielded because no extra interference shields, such as metal meshes or aluminium foil, are added to the cables.

The wires are then connected to a connector (such as the RJ45 connector of an ethernet cable).
Fibre optic cables, on the other hand, are made of thousands of very thin strands of pure glass, called optical fibres, inside an insulating jacket. Instead of using electrical signals, fibre optic cables use light to transmit data very quickly.

Fibre optic cables are largely replacing metal cables since they are more flexible and lighter and can transmit data over longer distances with lower rates of data loss. The most common application for fibre optic cables is in internet connections.

COPPER VS FIBRE
WIRELESS COMMUNICATION
As you know, wireless connections allow you to transfer data over a distance without using cables, wires or physical connectors. Most common wireless communication uses radio waves to send data from one point to another.
A transmitter on the sending end turns the signal into an electromagnetic radio wave. The antenna picks up the radio wave and the receiver turns the electrical signal back into data.
 Activity 7.1
Activity 7.1
Answer the following questions:
1.Briefly describe the difference between a workstation and a server.
2.List two functions of network software.
3.How do wireless networks connect devices in a network?
4.Provide two advantages of using fibre optic cable to connect to a network.
UNIT
7.2 Intranet vs internet
While they may sound like the same thing, there are actually a fairly large number of differences between the internet and an intranet. In this unit, you will learn about these differences as well as what an extranet and a virtual private network (VPN) are.
INTRANET VS INTERNET
An intranet is a private, web-based network that is only available to an organisation’s staff. Intranets work using internet protocols to share data and information across the network. To put it simply, an intranet is like a private internet. Very often, a company’s intranet will have information on it that the company does not want the public to have access to, such as employee contact details and calendars.
Intranets are also a valuable communication tool in a company as they allow all members of staff to work together, find information, create content and share tasks quickly and easily. Intranets act as a website and a communication channel together. Access to an intranet is limited to users who have been given usernames and passwords to connect with it.
The internet, on the other hand, is a massive network of networks with millions of computers connected to each other across the globe. All of these computers can communicate with each other as long as they are connected. By design, the internet is decentralised, meaning that it is not controlled by a single, central authority. Each computer, or host, is independent and the owner or operator of that host can choose which internet services to use and which local services they will make publicly available.
The internet itself is publicly accessible and is not the World Wide Web (WWW), which is simply a way to access information over the internet. Access to the internet is usually provided by ISPs.

INTRANET VS EXTRANET

HOW A VPN WORKS
VPNs are groups of computers (a network) connected over a public network (like the internet). Businesses use VPNs to allow their staff to connect to their internal networks without them being connected to the LAN (for example, if a staff member has to work in an office in Cape Town, they can connect to the main office in Johannesburg using a VPN).
VPNs can also be used to secure your computer’s internet connection to keep the data you are sending and receiving safe from unwanted access when you are using an internet connection you do not trust (like a Wi-Fi connection in a coffee shop). A VPN encrypts all the data your computer sends over an internet connection.
 Activity 7.2
Activity 7.2
1.Answer the following questions in your own words.
a.Define an intranet.
b.What are the main differences between an intranet and the internet?
c.What is the main purpose of an extranet?
d.What would you use a VPN for?
UNIT
7.3 Basic network security
In our modern age, more and more of our important and personal data is being stored digitally and hackers and other criminals want to get hold of that information. That is why it is extremely important that the networks we use daily are secured and protected.
In this unit, you will learn about the basics of passwords, usernames and access rights, and how those three factors combine to secure a network.
PASSWORDS
Passwords are the most basic form of network security. Passwords, at their core, are a secret string of letters, numbers and symbols created by users or generated by a computer to limit or restrict access to a system.
More often than not, you will need to pick your own password to make sure that it is something you can remember.
USERNAMES
Usernames are a unique identifier given to any person who uses a secure computer network. Usernames are also called an account name, login ID or user ID. Usernames are most commonly used with passwords and can be used on computers or websites.
ACCESS RIGHTS
On a computer, for example, a user may only have access to a personal folder where they can open, read, write, create and delete files and folders. A user with administrative rights can access all the files and folders on a computer and can make changes that will affect all users.
 Activity 7.3
Activity 7.3
Answer the following in your own words.
1.Read the following case study and answer the questions which follow:
Cyber-attacks: Protecting universities and solving cyber security issues
Oxford, Warwick, and Greenwich Universities are among many of the higher education institutes to have fallen victim to attacks in recent years, with hackers attempting to steal research data and documents. The problem has become acute enough to warrant the publication of cybersecurity guidance for universities and colleges by the UK Government’s National Cyber Security Centre (NCSC) recently.
No organisation today is immune from the threat of cyber-attacks. While we most often hear about breaches suffered by retailers, financial institutions and, since the infamous WannaCry ransomware attack in 2017, healthcare providers, many other types of organisations are becoming appealing targets for cybercriminals.
a.Define what a “hacker” is and distinguish between a “hacker” and a “cracker”.
b.Give THREE ways to secure information on a network.
c.Why would it be valuable for hackers to steal research data and documents?
d.What are the consequences of being a victim of a ransomware attack?
REVISION ACTIVITY
QUESTION 1: MULTIPLE CHOICE
1.1A private network that is only available to the organisation`s employees. (1)
A.Internet
B.WLAN
C.Intranet
D.LAN
1.2A network of computers covering a small area such as a school or office building. (1)
A.WAN
B.LAN
C.GAN
D.PAN
1.3All the computers that are connected to the network. (1)
A.Work stations
B.Servers
C.Input devices
D.Network software
1.4A network that uses radio waves to communicate rather than cable. (1)
A.WAN
B.LAN
C.GAN
D.WLAN
1.5A computer that provides shared resources, such as files and printers. (1)
A.NIC
B.Server
C.Workstation
D.Network security
QUESTION 2: TRUE OR FALSE
Choose the answer and write True or False next to the question number. Correct the statement if it is FALSE. Change the underlined word(s) to make the statement TRUE. (You may not simply use the word NOT to change the statement.)
a.If a network is not secured properly, the entire network will be infected should there be one infected computer. (1)
b.A PAN (personal area network) is designed to connect networks across large distances, for instance a province. (1)
c.In a LAN, networks are globally controlled, for easy changes and updates. (1)
d.An NIC (network interface card) allows a computer to communicate with a network. (1)
e.The main function of a workstation is to serve the information stored on it to the other connected computers. (1)
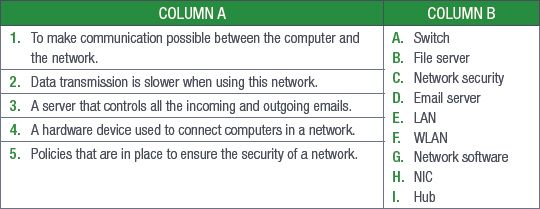
QUESTION 3: MATCHING ITEMS
Choose a term/concept from COLUMN B that matches a description in COLUMN A. Write only the letter next to the question number (e.g. 1-J). (5)
QUESTION 4: MEDIUM QUESTIONS
4.1Besides computers, name one other hardware device you might find connected to a network. (1)
4.2Give two reasons why a wireless network (WLAN) is better than a cabled network. (2)
4.3List two possible disadvantages of using a WLAN. (2)
4.4Provide two examples of servers that can be used in a network. (2)
4.5Briefly explain the following communication devices:
a.Modem (2)
b.Router (2)
QUESTION 5: SCENARIO-BASED QUESTIONS
Choco`s Chocolate Company sells chocolates to distributors as well as directly to the public. The company`s head office is in Cape Town with branches in Port Elizabeth, Durban and Johannesburg. Each branch has its own LAN, which communicates with head office.
5.1The company uses a LAN in all its branches.
a.Briefly explain what a LAN is. (2)
b.Give two advantages of using a LAN. (2)
c.Give two disadvantages of using a LAN. (2)
5.2Some of the employees have decided to communicate with their clients using IM.
a.Explain how IM works. (2)
b.Provide two reasons why the employees should be careful when using IM. (2)
5.3The company uses FTP for the electronic sharing of documents larger than 6 GB.
a.Why is it a good idea that the company uses FTP? (2)
b.Give two disadvantages of using FTP. (2)
TOTAL: [40]
AT THE END OF THE CHAPTER
|
Previous
Chapter 6: Social implications of hardware
|
Table of Contents |
Next
Chapter 8: Social implications of computer networks
|





