3.1 Overview of physical aspects of a network
|
Previous
Chapter 2: Software
|
Next
Chapter 4: Social implications
|
 CHAPTER OVERVIEW
CHAPTER OVERVIEW
| Unit 3.1 | Overview of physical aspects of a network |
| Unit 3.2 | Overview of network innovation |
 Learning outcomes
Learning outcomes
At the end of this chapter you should be able to:
- list and describe network communication and data transmission
- list and describe the physical limitations of networks
- describe network innovations. including VOIP, VPNs and location-based computing
- define and provide examples of location-based services websites.
INTRODUCTION
In this chapter, you will learn more about networks, and specifically the way in which data is transferred over a network. To understand data transfer, you will look at the different network hardware required, the limitations of networks and how data is transferred on different network sizes. Finally, the chapter will conclude by looking at a few interesting network innovations.
NETWORKS
In Grade 10, you learned that networks are incredibly powerful tools that most modern people and businesses depend on daily. Networks have thousands of different uses, including:
- sharing resources
- organising information
- connecting people
- providing access to entertainment.
However, it can also expose people to network crimes, advertising, spam, cyberbullying and abuse. Networks in general, and the internet, can also be addictive and make it difficult for people to disconnect from technology, which can result in more social isolation and depression.

Did you know
In 2016, Amazon Web Services used a sneakernet to transfer 50 petabytes (that is, 50 million gigabytes) of data by loading a truck full of storage devices and driving the data to a data centre. To download the same amount of data from the internet using a 100 MB fibre connection would take 250 years!
Activity 3.1 Revision activity
3.1.1You are considering setting up a Wi-Fi network to connect the devices in your office and have decided on the above layout.
A friend suggests setting up a wired network.
a.Define a network.
b.Give TWO reasons why you need a network.
c.State TWO disadvantages of having a computer network.
d.Which network is more suitable for home, give reasons.
UNIT
3.1 Overview of physical aspects of a network
A computer network refers to a group of two or more computing devices that are connected by a communication medium allowing the computers to communicate electronically. A computing device on a network is usually referred to as a node, being connected to one another, it allows nodes to exchange data with one another using a connection media between them. The links can be established either over cable media such as wires or via a wireless media such as Wi-Fi.
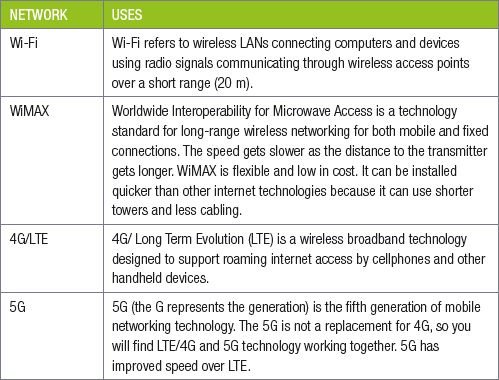
Table 3.1: Summary of different types of wireless media
Data transmission is supported by various pieces of hardware, media and devices, set up in a specific layout.
DATA TRANSMISSION
MEDIA
There are two types of networks, and three types of media to support them. These are:
WIRED NETWORKS
A wired network is a network that uses a physical media to transfer data between two or more nodes. The transmission medium for wired networks are Unshielded Twisted Pair (UTP) and Fibre optic cables.
WIRELESS NETWORKS
A wireless network consists of transmitters and receivers. Nodes connect wirelessly to these transmitters and receivers to complete the network. Home Area Networks are often Wireless Local Area Networks (WLAN).
The media needed to support these networks are:
- Radio waves (wireless network)
- Infrared


PHYSICAL LAYOUT (TOPOLOGY - STAR)
Every LAN has a topology, this is the way that the devices on a network are arranged and how they communicate with each other. The physical topology is the physical structure of the network in which workstations are connected to the network through the actual cables that transmit data. There are many different layouts but we will look at the star topology:
In a star network, the devices are connected to a central node, called a switch. Nodes communicate across the network by passing data through the hub. Two of the biggest advantages of a star topology is that new devices can easily be added to the network, and if any connected device breaks, it does not affect the rest of the network. The main disadvantage is if the switch fails then the entire network becomes unusable.

PHYSICAL LIMITATIONS (ACCESS AND BANDWIDTH)
Bandwidth refers to the amount of data that can be sent over a network in a specific amount of time. For example, an internet connection with high bandwidth (such as 100 Mb/s) allows you to download a large amount file quickly, while an internet connection with lower bandwidth (such as 512 Kb/s) will take a much longer time to download the same file.
A user’s account can have limitations restricting the user access to the network. Examples include time, bandwidth and storage access.
CONNECTION DEVICES
A few examples of connection devices include:
Network Interface Card (NIC): Most desktop computers have a built-in ethernet card, which would enable it to connect to a cabled network. Your laptop or smartphone would most likely have a built-in wireless NIC.
Modem: The purpose of a modem is to connect a computer or network to the internet.
Switch: The purpose of a switch is to connect many computers on the same, wired internal network and has the ability to direct network traffic to the correct port.
Router/bridge: The purpose of a router is to connect different types of networks using one device. This can include combining wired and wireless networks or connecting a LAN network to a WAN network. Many routers may contain a modem to connect to a telephone line.

Did you know
kB - kilobyte
kb - kilobits
Mb/s - megabits per second
kb/s - kilobits per second
 Activity 3.2
Activity 3.2
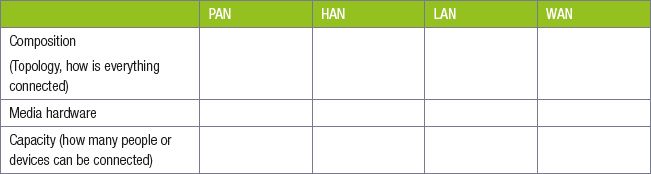
3.2.1In small groups populate the table to compare the composition, media and capacity of the different networks.
3.2.2Study the following representation of a network (from Google images) and answer the questions.
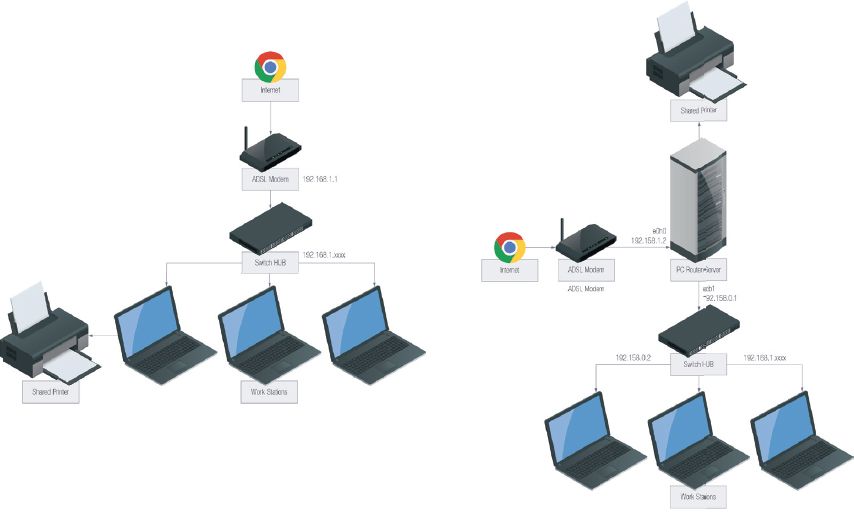
In the image it is shown that the network is used to share a printer (hardware) and Internet. List THREE other reasons for having a network.
3.2.3A star topology is used in this representation of a network.
a.Define the term topology.
b.Explain why the star topology is overall a popular choice.
c.List ONE disadvantage of a star network.
3.2.4Your next work-shadowing experience is to meet with management of the local Nestle factory who outsource their IT requirements to your friend’s IT business. They want to set up a network in their canteen for staff access. A network card is an example of an important hardware component in a network.
a.List TWO other hardware components that are needed for a network.
b.What is a network card used for?
3.2.5Differentiate between a router and a switch.
3.2.6Max has decided to use Wi-Max technology to connect to the Internet.
a.State TWO other technologies you could have used to connect to the Internet.
b.Justify your reason for choosing Wi-Max instead of any of the TWO ways mentioned in the above question.
c.Name the device that you will need to link your local network to the Internet.
UNIT
3.2 Overview of network innovation
Network technologies are constantly changing, with new technologies being invented each year. Whether it is lightbulbs that connect to your Wi-Fi network and change colour based on your smartphone settings (like the Phillips Hue), mesh wireless routers that instantly create a great wireless network (like Google WiFi), or car-to-car communication networks that allow driverless cars from driving into any other cars, new technologies will continue to change the way we live.
In this unit, you will learn about three network innovations that have proven their staying-power. These are:
- voice over internet protocol (VOIP)
- virtual private networks (VPN)
- location-based computing.
VOICE OVER INTERNET PROTOCOL (VOIP)
Voice over internet protocol (VOIP) is a technology that allows phone calls or video calls to be made over the internet. There are two main types of VOIP calls:
- VOIP to VOIP calls
- VOIP to phone calls
VOIP to VOIP calls can usually be made for free. To make these calls, both the person making the VOIP call and the person receiving the call must have an account with the same VOIP service (such as Skype, WhatsApp, Facetime or Discord). If you have access to a fast internet connection, this is a great way to contact someone for free.
VOIP to VOIP calls can even include multiple people in a chat room or conference call. For example, the application Discord allows you to open a permanent chat room and voice chat with your friends. Once created, you can join the room from your phone or computer and anything you say over your microphone will be broadcast to any friends connected to the same room.
The second type of VOIP calls are made between VOIP and a phone. These services usually cost money but are often significantly cheaper than making a normal phone call. You are also able to make these phone calls directly from your computer, which can be more convenient for some people. The application Skype allows you to make VOIP to phone calls, but there are also many private VOIP-to-phone service providers like Vox Telecom and InterExcel.
When talking about different types of networks, it is easy to get the words internet, intranet and extranet confused.
The internet is a global network that allows computers from around the world to communicate and share information (such videos or webpages). There is only one internet in the world and that is the internet that all computers share.

New words
mesh – a type of network in which a device (node) transmits its own data as well as serves as a relay for other devices (nodes)
virtual private network (VPN) – an encrypted connection over the internet from a device to a network
INTERNET VS. INTRANET VS. EXTRANET
In contrast to the internet, the intranet is a locked private network used to share information on a private network. Many businesses create intranets that give employees access to shared files and network resources. These network resources can include:
- Network printers
- Shared folders
- Network applications
Finally, the word extranet is used to refer to any network that combines an intranet with the internet. Many companies build extranets so that their employees can get the benefit of the intranet when they are not in the same physical space as the local network. For example, employees can use an extranet from home to access documents shared on their company’s intranet.
https://www.hyperoffice.com/blog/2018/06/20/intranet-examples/

Video
Animation showing how a VPN is used to anonymise and encrypt computer traffic. Something like: https://youtu.be/_wQTRMBAvzg?t=130


QR CODE
VIRTUAL PRIVATE NETWORK (VPN)
A virtual private network (VPN) is a computer connected to a VPN can access all the private network resources shared on the network (including printers and file servers), without physically being in the same area.
In the past, VPNs were mostly used by companies to allow employees to connect to their internal networks from anywhere in the country. This was useful for employees working from home, visiting clients, or working from a different office, and VPNs are still often used in this way.
VPNs allow people to access the internet anonymously and securely, no matter your geographical location in relation to the server. For example, if you log onto the American VPN server, internet companies would assume that you are in the USA.
LOCATION-BASED COMPUTING
Location-based computing refers to several different technologies that make use of geographical position to customise a user’s experience.
The six components required include:
1.Positioning system e.g. GPS (Global Positioning System)
2.Communication network for data transfer
3.Service and application provider e.g. Maps or Uber
4.Data and content provider
5.Mobile devices
6.User
This is simply one of the many ways in which location-based computing is used to improve our lives. Other uses include:
- Weather applications that tell you what the weather in your specific area will be, based on your location.
- Food ordering applications that use your location to deliver food directly to you.
- Car sharing services like Uber that use your phone’s location to find the nearest Uber driver, who will then pick you up and drop you off at the correct location.
All these technologies use a combination of GPS and mobile internet connections to improve the service they offer you.

New words
GPS – a system of satellites, computers, and receivers that allows land-, sea-, and airborne users to determine their exact location, velocity and time 24 hours a day in all weather conditions, anywhere in the world
 Activity 3.3
Activity 3.3
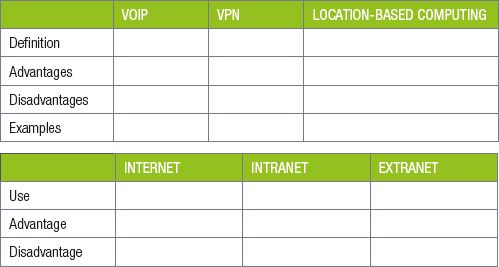
Complete the following tables comparing network innovations.
CONSOLIDATION ACTIVITY Chapter 3: Networks
1.Choose the correct answer.
a.VPN stands for...
A. Very Private Network
B. Virtual Protocol Network
C. Very Powerful Network
D. Virtual Private Network
b.The following types of network in ascending order with regards to their size:
A. LAN, PAN, WAN, HAN
B. PAN, HAN, LAN, WAN
C. WAN, PAN, HAN, LAN
D. HAN, PAN, WAN, LAN
c.A device that converts the data or signal from a computer to format that can be transmitted over a communication channel:
A. Router
B. Modem
C. Switch
D. Mouse
2.Choose the answer and write ‘true’ or ‘false’ next to the question number. Correct the statement if it is FALSE. Change the underlined word(s) to make the statement TRUE. (You may not simply use the word ‘NOT’ to change the statement.)
a.A LAN is a small network that is usually limited to a single building.
b.The internet is a global network that allows computers from around the world to communicate and share information (such videos or webpages).
3.Briefly explain the difference between a router and a switch.
4.What is the function of a modem in data communication?
5.Explain what a VPN is. Do not just expand on the acronym.
6.All the devices including the Satellite TV decoder, gaming console, mobile phones and tablets in the household will be connected in this setting by a multipurpose LTE router/modem.
a.What is the term used to describe this kind of network?
b.Give TWO advantages and TWO disadvantages of having a network.
c.What are the FOUR main functions of the multipurpose router/modem in this network?
d.Identify the topology that is employed in this environment.
7.You are offered the position of ICT manager of a new shopping mall. No ICT infrastructure has been put in place. You are tasked to help with implementation of ICT in the mall.
a.Explain to her FIVE main advantages of having a network for the mall.
b.Explain what is necessary for each machine to be connected to a network.
c.One of the buildings is set a bit back from the others in the mall. The owner of this shop is worried about connectivity.
i. The building is 150 m away from the mall. Name TWO connection methods which could be used to connect this building to the rest of the network.
ii. Should speed be a factor in the above question, which ONE of the connection methods would you suggest? Motivate your answer.
iii. The mall covers an area of 200 m by 350 m, all on one street block. What type of network is this considered to be? LAN or WAN?
|
Previous
Chapter 2: Software
|
Table of Contents |
Next
Chapter 4: Social implications
|


