10.1 Overview of security concepts
|
Previous
Chapter 9: Networks
|
Next
Chapter 11: Social implications
|
 CHAPTER OVERVIEW
CHAPTER OVERVIEW
| Unit 10.1 | Overview of security concepts |
 Learning outcomes
Learning outcomes
At the end of this chapter you should be able to:
- Explain the purpose and use of:
- encryption
- SSL
- certificates and security
- and firewalls.
INTRODUCTION
E-communication, or electronic communication, is a type of communication between people in the form of texting, signals, data, sounds, images, signs or intelligence sent via an electronic device. Some examples of e-communication include email, text messages, social media messaging and image sharing. Security measures that can be taken to protect e-communication from cyber criminals is discussed in this Chapter.
 Case Study Cyber-attacks on government websites
Case Study Cyber-attacks on government websites
There are concerns about the lack of security measures on government websites after a cyber-attack on the official Presidency website. According to Independent Online, the Presidency’s website was hacked on Saturday by an unknown group who posted: “Hacked by Black Team. Sahara is Moroccan. And Morocco is ur Lord!”.
Information technology security specialists say that if it was so easy to attack a website like that of the Presidency, what other computer systems and websites with sensitive information will be hacked. There have been previous hacks of government websites such as, the departments of Education and Home Affairs which exposed the data of more than 30 million South Africans and SAPS where sensitive information, including that of whistle-blowers, had been compromised.
Cybercriminals are getting more advanced and find ways to hack websites where there are vulnerabilities in software. This cyber-attack caused South Africans to think twice before they shared any personal information with government entities online.
Professor Basie Von Solms, director of the Centre for Cyber Security at the University of Johannesburg said, ‘What could help was the implementation of the Protection of Personal Information Act which required organisations to put in measures that would ensure people’s data is kept safe and follow international best practices.’
UNIT
10.1 Overview of security concepts
Since e-communication is online there is a chance of cyber criminals getting hold of the information. Security measures that can be taken are discussed in this Chapter.
ENCRYPTION
Encryption is the process of encoding a message or information in such a way that only authorised parties can access it. With encryption, any data sent between two computers is changed from something that is useful to encrypted data that meaningless and extremely difficult for unauthorised parties to decrypt. The only way to turn the encrypted data back into useful data is to know the encryption key, which is only known by the receiving computer. The encrypted message, data or information can only be decoded by another entity if they have access to a decryption key.
PURPOSE OF ENRYPTION
By encrypting personal data such as usernames and passwords, websites provide an extra layer of protection for users. With encryption, even if the website is hacked and its database stolen, the hackers cannot see the usernames and passwords without the encryption key. Since the encryption key is stored separately, the encrypted data remains safe.

QR CODE
HOW DOE ENCRYPTION WORK?
Imagine entering your password on your online banking website. A clever hacker might place himself in-between you and your bank. Any messages you send to your bank (such as your password), therefore first passes through the hacker’s computer before going to your bank. If your data is not encrypted, the hacker can easily read your password before sending it to your bank. Neither you, nor your bank, might know that the password is stolen, and the hacker can use the password to steal your money!
Websites that have HTTPS (Hypertext Transfer Protocol Secure) in theirURL are using encryption. Most online services today also encrypt personal user information in their databases, which means that, even if a hacker gets access to the database, they cannot just read all the user’s usernames and passwords. Instead, they will only see encrypted usernames and password, which useless to them.

QR CODE
SSL (PRIVATE AND PUBLIC)
When you enter data on a normal HTTP website, the data is sent to the website as plain, unencrypted text. Hackers can use several different techniques to intercept this message and gain access to your username and password. This is especially problematic when you are doing online shopping, since anyone intercepting your purchase message can steal your credit card information!
To stop this from happening, websites can use HTTPS to encrypt any traffic sent from the user to the website, and from the website to the user. HTTPS does this by using SSL (or Secure Sockets Layer).
PURPOSE OF SSL (SECURE SOCKET LAYER)
SSL adds a security layer to any web page. Any message that is sent to the website first passes through the security layer (which encrypts the message) before travelling to the website. When the website returns information, this information is once again sent through the secure layer and encrypted before being sent to the user. Because of SSL, anyone who intercepts information sent or received on an HTTPS page will simply receive a scrambled, encrypted message that is useless to them.
To see if a website is secure, you can look at the protocol it uses as well as the small lock icon next to its URL.
SSL (PUBLIC AND PRIVATE KEY)
If a user needs a website’s encryption key to decrypt any information he or she receives, and the website needs the user’s encryption key to decrypt any information they send, then how do they share these keys? Websites use public and private keys to encrypt information.
PUBLIC KEY
The public key is public, which means that all the messages you send and all information you submit on the Internet contains this public key. Even though hackers can easily see this public key, they cannot use it to unlock information encrypted with the public key. To unlock this information, they need your private key. Unlike your public key, your private key is kept a secret by your computer and never shared with anyone.

Animation
Animation showing information locked with a public key then unlocked with a private key, then locked with a private key and unlocked with a public key.

Whenever your computer visits a new website, you exchange public keys. You send the website your own public key, and the website sends its public key to you. When the website then sends you information, it encrypts it twice: Once with website’s private key and once with your public key.

Animation
Animation showing information locked with user’s public key and locked with the website’s private key. This information is then sent from the website to the user. The animation should show the information having two locks on it at the end.

Since the information has been encrypted twice (with the website’s private key and with your public key), you will need two keys: The website’s public key (to decrypt its private key)
YOUR PRIVATE KEY (TO DECRYPT YOUR PUBLIC KEY)
Since the website’s public key is public, you (and any hackers) know the public key and can remove the first set of encryptions using the public key. However, since only you know your own private key, only you can remove the last set of encryptions from the information. This means that only your computer can fully decrypt the information to understand it.
When you return a message to the website, you encrypt it using your own private key and the website’s public key before sending it. The website therefore needs your public key (which everyone has), and its own private key (which only it has) to decrypt the information. In this way, you can send information to the website so that only it can decrypt it.

Animation
Animation showing the information locked twice being unlocked with the website’s public key and the user’s private key, and then becoming legible.

CERTIFICATES AND SECURITY
Before your browser can encrypt and send any data to a website using SSL, it first requests the website’s SSL certificate. Websites use this certificate to prove their identity. To obtain an SSL certificate, websites must apply for a certificate with a certification authority.
All SSL certificates should contain the following information:
- The domain name (or subject) the certificate is valid for
- The certificate authority who created (or issued) the certificate
- The dates the certificate is valid for
This is shown in the figure in the margin.

PURPOSE OF SSL CERTIFICATES:
Before you can send any personal or encrypted information to a website, your browser will first compare the certificate it receives with the certificate from the certification authority. If it finds any mistakes, or receives an outdated certificate, it will warn you that the certificate it received is not legitimate and stop you from sending personal information to the website.
SSL therefore not only ensures that any information you send and receive is encrypted, by using certificates, it also ensures that the encrypted information is only sent to the correct websites (and not to malicious or phishing websites).
FIREWALLS
On computers, firewalls prevent malicious users and viruses from sending data to and receiving data from your computer. There are three general types of firewalls:
- Software firewalls that are installed on the user’s computer and protects a single computer.
- Software firewalls that are installed on a server or router that protects all the computers on the network.
- Hardware firewalls that are installed between a local network and the internet and protects all the computers on the network.
Firewalls work by allowing any data you request or send to go through the firewall, while blocking any unrequested information from passing through the firewall. This allows you to access the internet and use it as normal but stops malicious users on the internet from sending viruses to your computer. Whenever you run a new program that uses the internet on your computer, your firewall will ask you whether to allow this program to send and receive data.
Today, most operating systems have a built-in firewall. This means you do not need to worry about installing a separate firewall. Instead, you should make sure that you only allow programs you to pass data through the firewall.

QR CODE
 Activity 10.1
Activity 10.1
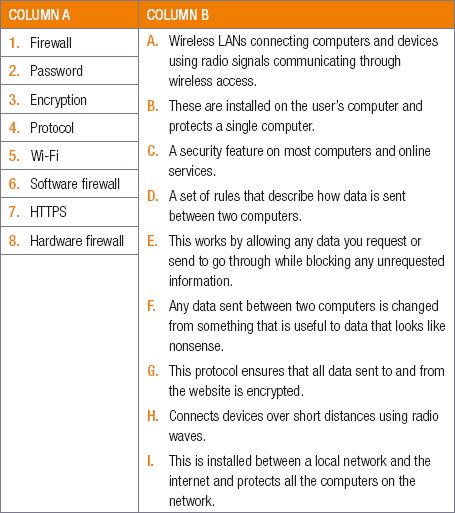
10.1.1Match the COLUMN A with the correct answer in COLUMN B. Write down only the question number and the matching letter in COLUMN B.
10.1.2Look at the picture below that shows statistics on security and answer the following questions.
a.Who would benefit the most from encryption? Why?
b.In your opinion, does all data need to be encrypted? Explain.
c.Why do you need to install security on your devices?
d.What security can be installed on your devices?
e.What do you find the most interesting and worrying about the statistics? Explain.

CONSOLIDATION ACTIVITY Chapter 10: E-communications
1.A password is used to protect your computer from others accessing it. Answer the following questions regarding security of a computer.
a.Explain how using a password for online services can protect you.
b.List THREE ways to make your password secure.
c.Explain how firewalls protect your computer.
d.List THREE types of firewalls.
e.What is encryption?
f.What do most websites use to enable encryption?
2.Give ONE word/term for each of the following descriptions. Write only the word/term next to the question number in your homework book.
a.Before your browser can encrypt and send any data to a website using SSL, it first requests the website’s _______
b.To stop hackers from intercepting personal information, websites can use HTTPS to encrypt any traffic sent from the user to the website, and from the website to the user. HTTPS does this by using _______, which adds a security layer to any web page.
c.The process of encoding a message or information in such a way that only authorised parties can access it.
d.The encrypted message, data or information can only be decoded by another entity if they have access to a __________
3.Travel agents must be able to conduct business from their office building or by using their mobile office. As most of the business is conducted online, for example, customers need to book and pay online, they must have access to the Internet.
a.Online transactions are encrypted. Explain the term encryption.
b.How do websites use encryption to secure the site?
c.Online security methods include the use of a public and private key encryption. Briefly explain the difference and purpose of these keys?
4.The AmaNdlovhu Company plans to provide various services to members of the media during the Soccer World Cup. To make sure that no other journalist can steal their data, the media people want to have SSL connections to some websites.
a.What does SSL stand for?
b.What is an SSL certificate and how does it work?
c.Almost all computer security relies on passwords. State THREE rules to follow when creating a password that will be very secure.
5.What is a firewall?
6.Briefly explain how a firewall works.
7.Explain the THREE general types of firewalls you can get.
8.Briefly explain what encryption is.
9.Give an example of how a bank uses encryption.
10.An important part of a network is a firewall. Name TWO ways that a firewall protects your computer.
11.Explain the THREE general types of firewalls you can get.
12.Briefly explain what encryption is.
13.Give an example of how a bank uses encryption.
|
Previous
Chapter 9: Networks
|
Table of Contents |
Next
Chapter 11: Social implications
|




